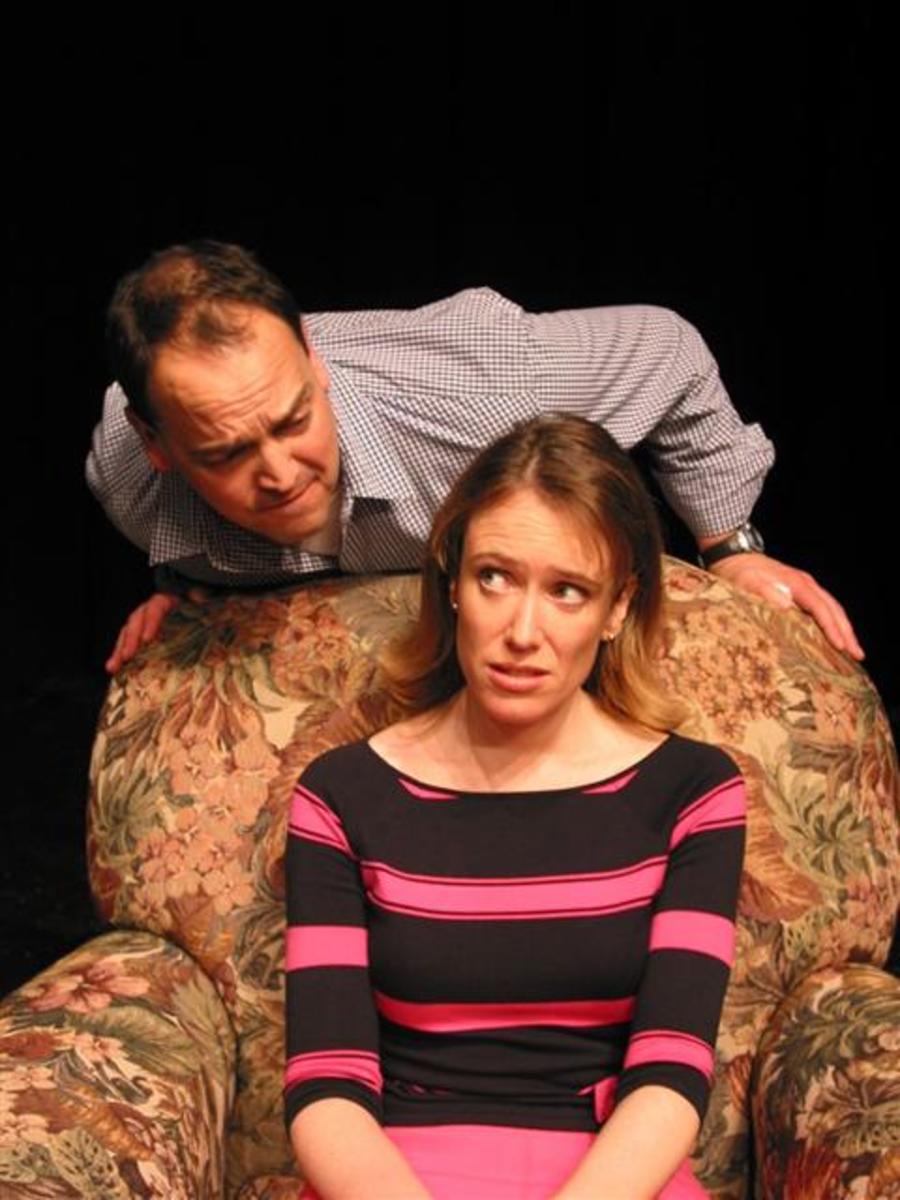
What is Relational Aggression?

Understanding the "Mean Girls" Mentality
The term “relational aggression” (RA) refers to non-violent attacks, such as name-calling, manipulation, ignoring or excluding someone from events or activities. It differs from traditional aggression in that while it is rarely physical it may lead to physical aggression if not controlled.
RA most often falls into two categories ignoring and intimidation.
Bullies employ the ignoring type of aggression when they purposefully exclude a person from activities and claim things such as “there is no rule against” not inviting the other students to something, notes the Suffolk Public Schools website (2011). Although the primary intimidation tactic was name-calling in the schoolyard in the past, the modern bully uses electronic devises to invade personal space and intimidate the victim (Gomes, 2007, p. 510).
Aber, Brown and Jones (2003) as cited in Boyer (2008) notes that while boys are more likely to use physical aggression intentionally, girls are more likely less likely to engage in physical aggression than boys (Behmm- Morawitz & Masto, 2008, p.133), and are more likely to use subtle forms of intimidation and RA (Boyer, paragraph 1). The difference between the methods of boys and girls is due to the belief that physical acts will be caught and punished, whereas more emotional tactics won’t be caught as easily (Boyer, paragraph 1). While some bullies pick on the victim due to a differences in clothing or being “different”, Boyer notes that much girl-to-girl aggression “stems from competition for male attention” (paragraph 1).
Video- "Mean Girls: Four Ways to Respond"
Students’ feelings on RA is complex notes a study by Goldstein & Tisak (2010). Although students believed that forms of RA such as gossiping was “very wrong”, excluding people from activities was seen as “somewhat acceptable” (p. 471).
While exclusion from activities may be severe at school, the most common form of RA in modern society stems from interactions with electronics, in the form of cyberbullying. Stomfay-Stitz & Wheeler (2007) characterizes cyberbullying as posting harmful messages and photos on social media, sending repeated rude and hurtful emails, and send threats of physical harm (paragraph 4). Cyberbullies often create personas with the specific intent of harassing the victim, and may even try to impersonate the victim themselves to damage remaining relationships with other friends. Unlike traditional bullying tactics, cyberbullying enters the personal space of the victim, invading their computer, cell phone and the public areas of social media sites. Instead of only the victim and maybe a few classmates witnessing the harassment in the school yard, cyberbullying is visible to an unlimited number of people, 24 hours a day 7 days a week (Department for Children, Schools and Families, 2007, p. 14).
The well-known case of Megan Meier — a 13 year old who committed suicide after being cyberbullied on her MySpace account — testifies to the problems that can stem from comments over the Internet (Megan Meier Foundation). Not only does the content of the comments scar the victim emotionally, but also it leaves the victim to distrust people in general, since they do not necessary know who sent the hurtful message.
Books on Relational Aggression
Resources
Behm-Morawitz, E., & Mastro, D. E. (2008). Mean girls? The influence of gender portrayals in teen movies on emerging adults' gender-based attitudes and beliefs. Journalism & Mass Communication Quarterly , 85(1), 131-146. Retrieved from EBSCOhost .
Boyer, W. (2008). Girl-to-girl violence: the voice of the victims. Childhood Education . 84 (6). Retrieved from Factiva.
Goldstein, S. and Tisak, M. (2010). Adolescents’ social reasoning about relational aggression. Journal of Child and Family Studies . 19(4) 471-482. Retrieved from EBSCOhos t.
Gomes, M. (2007). A concept analysis of relational aggression. Journal of Psychiatric & Mental Health Nursing , 14(5), 510-515. Retrieved from EBSCOhost .
Herrenkohl, T., Catalano, R., Hemphill, S., & Toumbourou, J. (2009). Longitudinal examination of physical and relational aggression as precursors to later problem behaviors in adolescents. Violence and Victims , 24(1), 3-19. Retrieved from EBSCOhost .
Megan Meier Foundation. (2011). “Megan meier’s story.”
Stomfay-Stitz, A. & Wheeler, E. (2007) Cyberbullying and our middle school girls. Childhood Education . (83) 5. Retrieved from Factiva.
Suffolk Public Schools. (2011). “Mean girls- realities of relational aggression.” Retrieved online on July 7, 2011.